Pattern · Energy · May 2026
Building a regulator-grade voltage audit trail a regulator will accept months later
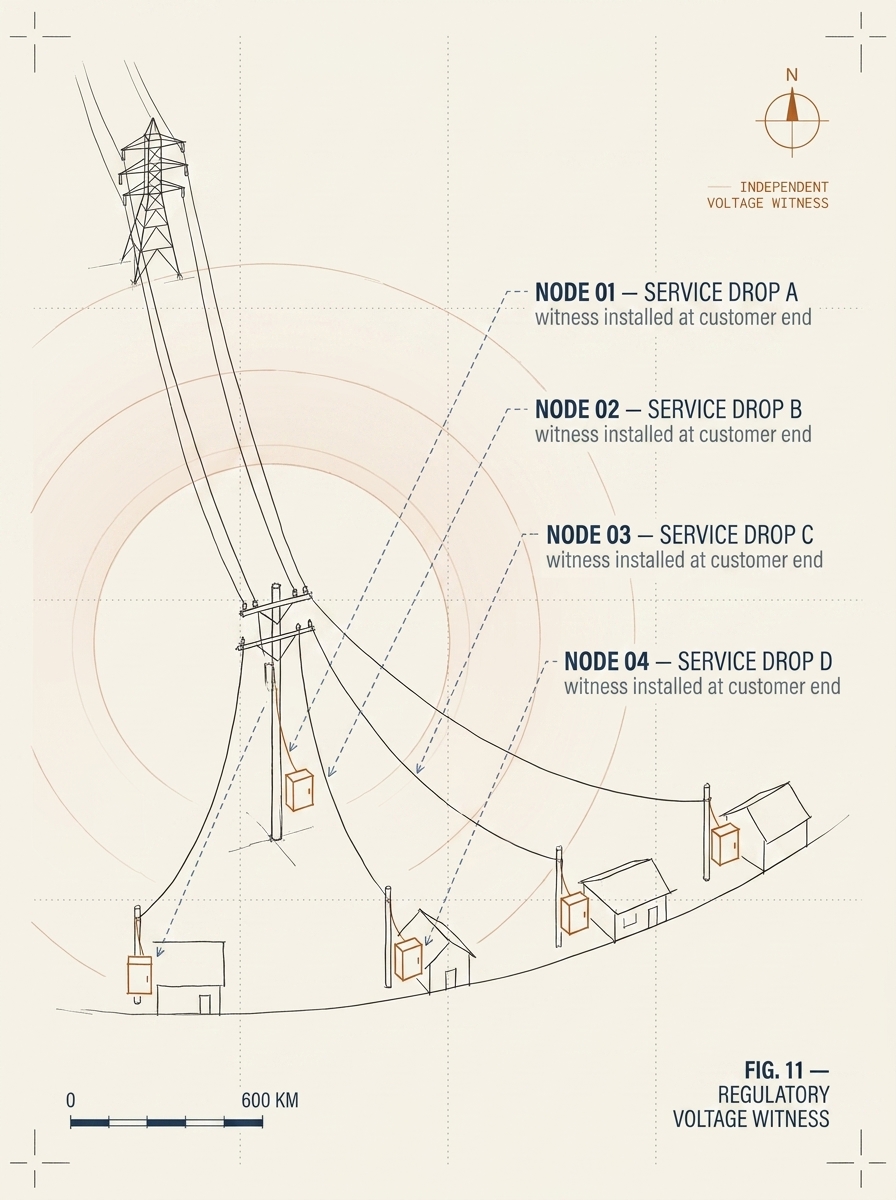
How we shipped independent voltage-presence witnessing at the customer end of a distribution network — so when the regulator audits a service-band claim six months after the fact, the evidence stands without depending on the distribution operator's own systems.
The situation
A regulator overseeing a distribution operator faced an escalating compliance problem. The operator was billing customers under a service-based tariff regime — different bands paying different rates for guaranteed daily supply hours. The regulator suspected that the operator was implementing substation-level load shedding to evade feeder-level monitoring: collecting Band A tariffs for guaranteed long-hour service, while delivering Band C service to specific customers.
The operator’s own metering infrastructure could not resolve the dispute. The readings were operator-controlled, operator-stored, and operator-verifiable — and that was the problem. A regulator cannot prosecute non-compliance using only the data the regulated party produces. The regulator needed an independent measurement source: deployed at the customer end of the line, below the level where the operator could selectively cut supply, with cryptographic proof that the measurements were unaltered.
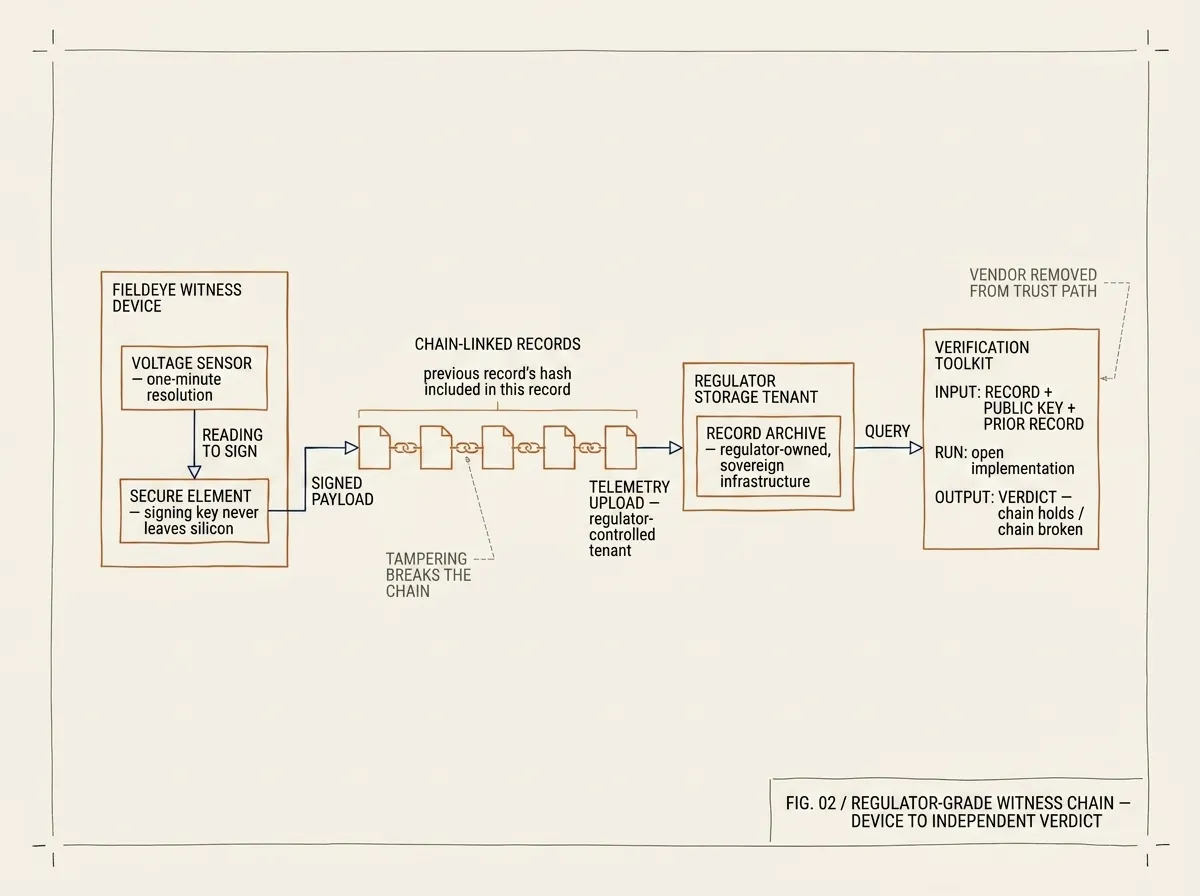
FIG. 02 / REGULATOR-GRADE WITNESS CHAIN — every reading is signed at the silicon layer and chain-linked to the prior record. The chain breaks if anything is tampered with. Verification is open and reproducible — the vendor is not in the trust path.
What we built
We deployed FieldEye voltage witness instruments at a sample of customer service drops across the operator’s franchise area. FieldEye does one thing: it attests, at one-minute resolution, to the presence or absence of mains voltage at the service drop. Each one-minute record is signed at the silicon layer using a key that lives in the device’s secure element and never leaves it. Each record is sequenced — its payload includes the cryptographic hash of the previous record from the same device. Tampering with the device, or with the storage, is detectable because the chain breaks.
Telemetry shipped to a regulator-controlled storage tenant — not the operator’s. The regulator’s expert witness was given the verification toolkit: a small open implementation that takes a record, the device’s public key, and the prior record, and returns a verdict on the chain. The verification step is reproducible and does not depend on us, on the operator, or on any vendor remaining in business.
For the first compliance hearing after deployment, the regulator submitted the operator’s billing claim against the FieldEye record set for the relevant feeders. The expert witness re-ran the verification independently. The chain held; the discrepancy between the operator’s claimed service hours and the actual measured hours was incontrovertible.
How independence was maintained
Three architectural decisions kept the deployment defensible. The signing key never left the device — not in firmware updates, not in over-the-air configuration, not in the manufacturer’s testing process. The telemetry storage was regulator-owned, in the regulator’s chosen sovereign infrastructure; we did not custodian the data and could not have produced it under subpoena even if asked. The verification toolkit was open and reproducible — there was no proprietary verification step that bound the regulator to us.
This last point mattered for the regulator. A toolchain that requires the vendor to certify each reading is a toolchain the operator can be invited to mistrust. A toolchain where the verification is open and the inputs are cryptographically self-describing removes the vendor from the trust path entirely.
What it produced
The operator’s compliance posture changed within a single regulatory cycle. Service-band claims started to align with measured service hours because the operator could no longer rely on selective load-shedding being invisible. Customer complaints about Band A tariff for Band C service dropped sharply. The regulator stopped asking for vendor attestations and started asking for the verification toolkit’s output directly.
The operational costs were modest. The hardware is purposefully inexpensive per unit so that wide deployment is feasible — the entire deployment fleet costs less than a single contested hearing it would have replaced.
What this pattern is good for
This pattern fits when three things are true: a regulator (or a customer in a contractually similar position) needs evidence the regulated party cannot manufacture, the contested measurement is one a small dedicated instrument can witness independently, and there is appetite for a phased deployment that prioritizes the highest-dispute customer points first.
If the regulator already has independent measurement infrastructure, the upgrade is unnecessary. If the contested fact requires complex multi-variable measurement (not just voltage presence, but power-factor correctness or harmonic content), the simple witness model isn’t sufficient and the pattern needs extension. Otherwise: 12–18 weeks per deployment phase, with each phase ending in a re-verifiable evidence chain.
Recognise this pattern?
Tell us about yours.
If your problem rhymes with this one, scoping a project usually takes us less than a week. References available under NDA.
Talk to an engineer →